Unable to find what you're searching for?
We're here to help you find itmin.pngL.jpg)
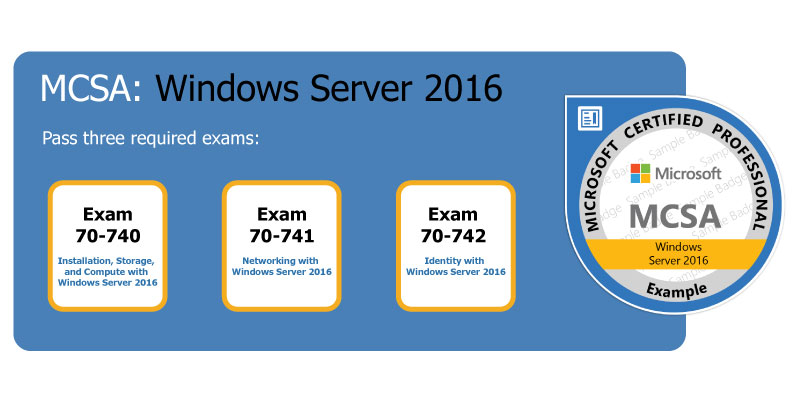
Microsoft offers many notable certifications out of which Microsoft Certified Solutions Associate or MCSA Training Certification trains you in skills necessary to become a computer network specialist or a computer systems administrator. Take a look at a few mcsa interview questions along with answers which are generally asked to Professionals.
Application partitions are directory partitions that are replicated to domain controllers. These are part of the Active Directory system. Domain controllers included in the process of directory partitions have a replica of that partition. The values and attributes of application partitions can lessen replication traffic. The application partitions can focus only on one domain in the domain area unlike the domain directory partitions. This makes them more available and redundant.
Also Read: A Complete Guide for MCSA Certification
The Active Directory database is stored on domain controllers and is accessible by network applications. All domains can be domain controllers and keep a copy of the Active Directory database in C:\windows\Ntds\Ntds.dit
Read only domain controller and Fine Grain Password Policy
Also Read: Interview Question and Answers for MCSA SQL Server Professionals
Windows Server Backup is a feature released for the Windows 2008 that provides a number of solutions on backing up the data on your computer in case of a system failure or any other issue. Windows Server Backup can backup a few files to a whole server. The server backup is accessible through command lines and a management console.
Also Read: A Storehouse of Benefits – MCSA: Windows Server 2016
A pass through disc is a physical disc used for storing virtual discs and it has a disc format and file system.
Synthetic drives are different and better than the emulation ones in their functions. They don’t imitate another program but, create another hardware complex device on a virtual platform.
Desktop virtualization is a logical procedure to isolate and extract the OS or system from the client that is ready to access it. There are many types of desktop virtualizations some of which include virtual machines while some do not. If the operating system is locally controlled, users have to access their desktop through a network relating to a remote display protocol. The processing of the desktop virtualization is done in a data center. So, applications like tablets can join Host virtual machine. This virtual machine can be accessed by an individual and can be personalized the way he wants it. This is the most common and simplest way of accessing and using a desktop virtualization.
BranchCache™ is designed to improve application responsiveness and reduce WAN link utilization so that the servers can be accessed from remote locations easily. The remote computer uses cache of data that is maintained locally to reduce traffic over a LAN link. The cache can be stored on a server in the branch (Hosted Cache mode) or can be distributed across client computers (Distributed Cache mode).
Direct Access enables users to access the websites, applications and internal network file shares securely without the need to connect to a virtual private network (VPN). An internal network is also called a private network or intranet. Every time a Direct Access-enabled computer connects to the Internet, even if this happens before the user logs on, Direct Access sets up bi-directional connectivity with an internal network. Users do not have to think about connecting to the intranet. The remote computers can be managed outside the office by the IT administrators, even when the computers are not connected to the VPN.
Microsoft Dynamic Access Control or DAC is a data governance tool in Windows Server 2012 that allows administrators control access settings. It uses centralized policies to permit administrators to review who has access to individual files. Files can be classified manually or automatically.
Also Read: Tips to Prepare for the New MCSA: Windows Server 2016 Certification

Anvesha Jain has a great variety of knowledge in the education industry with more than 3 years of experience. He has also done work with many educational institutes as a Career counsellor. He also likes to write blogs on different topics like education and career guidance