Unable to find what you're searching for?
We're here to help you find itCertified SOC Analyst v1 (CSA) Course Overview
The Certified SOC Analyst (CSA) course is a comprehensive program designed to prepare learners for the dynamic challenges in a Security Operations Center (SOC). This course is aimed at enhancing the essential skills required to identify, analyze, and respond to security incidents.
Module 1 lays the foundation by explaining SOC Fundamentals and delves into the critical components of SOC, including People, Processes, and Technology, and discusses strategies for SOC Implementation. Module 2 takes a deep dive into understanding Cyber Threats, network, host, and application-level attacks, Indicators of Compromise (IoCs), and the hacker's attack methodology. In Module 3, learners explore the intricacies of incidents, events, and the importance of both local and centralized Logging.
Module 4 advances into SIEM solutions, deployment strategies, and use cases for detecting various types of incidents, while Module 5 enhances detection capabilities through insights into Threat Intelligence sources and strategies. Finally, Module 6 equips learners with a robust understanding of Incident Response, covering the full spectrum of responding to diverse security incidents, ensuring a thorough preparedness for real-world SOC operations.
By completing the CSA course, learners will be well-versed in the practical aspects of security operations, making them valuable assets in protecting organizations' digital infrastructure.
Successfully delivered 79 sessions for over 215 professionals
Purchase This Course
USD
View Fees Breakdown
| Course Fee | 2,730 |
|
Total Fees (with exam) |
2,730 (USD) |
USD
View Fees Breakdown
| Course Fee | 2,100 |
|
Total Fees (with exam) |
2,100 (USD) |
USD
View Fees Breakdown
| Flexi Video | 16,449 |
| Official E-coursebook | |
| Exam Voucher (optional) | |
| Hands-On-Labs2 | 4,159 |
| + GST 18% | 4,259 |
|
Total Fees (without exam & Labs) |
22,359 (INR) |
|
Total Fees (with Labs) |
28,359 (INR) |
Select Time
Select Date
| Day | Time |
|---|---|
|
to
|
to |
♱ Excluding VAT/GST
You can request classroom training in any city on any date by Requesting More Information
Inclusions in Koenig's Learning Stack may vary as per policies of OEMs
Scroll to view more course dates
♱ Excluding VAT/GST
You can request classroom training in any city on any date by Requesting More Information
Inclusions in Koenig's Learning Stack may vary as per policies of OEMs
Suggestion submitted successfully.
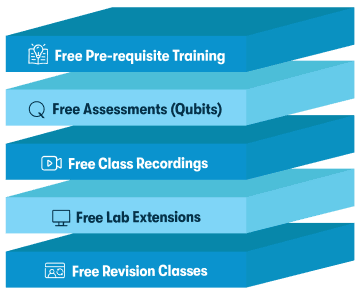
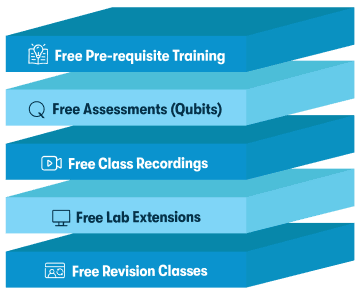
Koenig Learning Stack
Inclusions in Koenig's Learning Stack may vary as per policies of OEMs

