Unable to find what you're searching for?
We're here to help you find itCertified Penetration Testing Professional v1 (CPENT) Course Overview
The Certified Penetration Testing Professional (CPENT) course is a comprehensive program designed for individuals looking to enhance their skills in the field of ethical hacking and penetration testing. The course delves into advanced concepts and methodologies that are pivotal for conducting thorough and effective penetration tests.
Module 1 sets the stage with an Introduction to Penetration Testing and Methodologies, covering essential concepts, guidelines, and recommendations to follow during a penetration test. In Module 2, learners delve into the Penetration Testing Scoping and Engagement Methodology, learning how to properly scope and engage with clients, including legal aspects and communication strategies.
As the course progresses, students will explore various penetration testing techniques through modules focusing on Open Source Intelligence (OSINT), Social Engineering Penetration Testing, Network Penetration Testing for both external and internal networks, and tackling perimeter devices. Modules on Web Application Penetration Testing and Wireless Penetration Testing Methodology provide in-depth knowledge for testing different types of applications and wireless networks.
Specialized areas such as IoT Penetration Testing, Cloud Penetration Testing Methodology, OT/ICS/SCADA Penetration Testing, and Binary Analysis and Exploitation are also covered, equipping learners with the ability to test and secure a wide range of systems. The course concludes with Module 12, which focuses on Report Writing and Post Testing Actions, ensuring that participants can effectively communicate their findings and recommendations.
Overall, the CPENT course is designed to offer a real-world approach to penetration testing, providing learners with the skills required to perform multi-layered and complex penetration tests, ultimately preparing them for successful careers in cybersecurity.
Successfully delivered 67 sessions for over 141 professionals
Purchase This Course
USD
View Fees Breakdown
| Course Fee | 3,850 |
|
Total Fees (with exam) |
3,850 (USD) |
USD
View Fees Breakdown
| Course Fee | 2,950 |
|
Total Fees (with exam) |
2,950 (USD) |
USD
View Fees Breakdown
| Flexi Video | 16,449 |
| Official E-coursebook | |
| Exam Voucher (optional) | |
| Hands-On-Labs2 | 4,159 |
| + GST 18% | 4,259 |
|
Total Fees (without exam & Labs) |
22,359 (INR) |
|
Total Fees (with Labs) |
28,359 (INR) |
Select Time
Select Date
| Day | Time |
|---|---|
|
to
|
to |
♱ Excluding VAT/GST
You can request classroom training in any city on any date by Requesting More Information
Inclusions in Koenig's Learning Stack may vary as per policies of OEMs
Scroll to view more course dates
♱ Excluding VAT/GST
You can request classroom training in any city on any date by Requesting More Information
Inclusions in Koenig's Learning Stack may vary as per policies of OEMs
Suggestion submitted successfully.
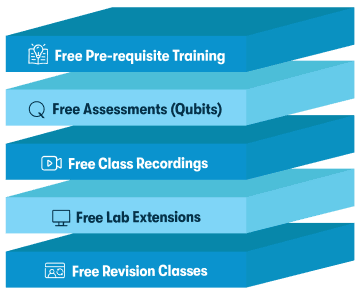
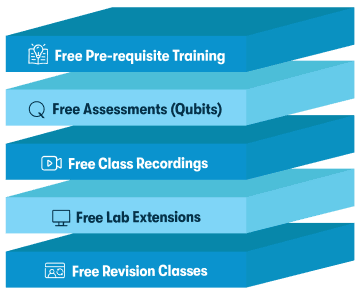
Koenig Learning Stack
Inclusions in Koenig's Learning Stack may vary as per policies of OEMs

